SOC as a Service: How Companies Can Improve Their Security Maturity Without Increasing Complexity
Maturity in information security is no longer a competitive advantage; it has become a basic requirement for companies of all sizes and across all industries. Cyberattacks are becoming more frequent, more sophisticated, and more targeted, while IT environments have become hybrid, distributed, and difficult to manage. In this scenario, many organizations know they need to evolve their security posture, but they face a recurring problem: how to increase the level of protection without adding more operational complexity, unpredictable costs, and dependence on highly specialized labor?
This is precisely where SOC as a Service (SOCaaS) establishes itself as one of the most effective strategies for improving cybersecurity maturity in a structured, scalable, and sustainable manner.
In this article, you’ll learn what SOC-as-a-Service is, why it has become essential for modern businesses, what challenges it addresses, and how this approach enables organizations to achieve a high level of security without overburdening the IT department.
The Challenge of Cybersecurity in Modern Businesses
In recent years, the attack surface for businesses has grown exponentially. On-premises environments coexist with the public cloud, private cloud, SaaS applications, remote users, personal devices, and third-party integrations. At the same time, attacks have shifted from being opportunistic to becoming surgical, persistent, and highly lucrative, such as ransomware, targeted phishing, vulnerability exploitation, and supply chain attacks.
Given this situation, many companies face challenges such as:
- Lack of continuous visibility into security incidents;
- Difficulty in detecting threats in real time;
- Overreliance on standalone tools (SIEM, EDR, firewall, etc.);
- Shortage of security professionals;
- High cost of maintaining an internal SOC infrastructure;
- Reactive processes, rather than preventive ones.
These factors directly impact security maturity, leaving the company vulnerable even when it invests in technology.
What is information security maturity?
Security maturity is not solely about the number of tools implemented, but rather about a company’s ability to prevent, detect, respond to, and recover from incidents consistently and effectively.
Companies with low maturity levels generally operate reactively: they only discover incidents after the damage has already been done. More mature organizations, on the other hand, rely on continuous processes for monitoring, event analysis, incident response, and continuous improvement.
Among the key pillars of security maturity are:
- Continuous threat monitoring;
- Intelligent event correlation;
- A rapid and coordinated response to incidents;
- Clear governance, processes, and metrics;
- Compliance with standards and regulations;
- People, processes, and technology working together seamlessly.
And that is exactly where SOC-as-a-Service comes in.
What is SOC as a Service (SOCaaS)?
SOC-as-a-Service is a model in which a company outsources the functions of a Security Operations Center to a specialized provider. Instead of setting up a complex internal infrastructure—which is costly and difficult to maintain—the organization gains access to a dedicated team of experts, advanced technologies, and established processes, operating 24/7.
In practice, SOC as a service is responsible for:
- Continuously monitor the IT environment;
- Collect and correlate security logs and events;
- Detect suspicious behavior and real threats;
- Investigate incidents;
- Implement response plans;
- Support the containment and mitigation of attacks;
- Generate security reports and metrics.
All of this is done in a centralized, standardized manner and in line with industry best practices.
Read more at: soc-why-it-has-become-essential-for-business-security-and-continuity/
Why is setting up an in-house SOC so complex?
Many companies initially consider setting up an in-house SOC, but they quickly realize the challenges involved. A traditional SOC requires:
- Significant investment in tools (SIEM, SOAR, EDR, NDR, etc.);
- A highly specialized team, available 24/7;
- Ongoing training to keep pace with new threats;
- Well-defined and up-to-date processes;
- High fixed costs and limited scalability.
Furthermore, the shortage of security professionals in the market makes the operation even riskier. A single staff turnover can jeopardize the continuity of monitoring.
The result is that, even after significant investments, many companies end up with an underutilized, incomplete, or inefficient SOC.
How SOC-as-a-Service enhances maturity without increasing complexity
The key advantage of SOC-as-a-Service lies in its ability to deliver a high level of security maturity without passing the complexity on to the customer.
Here's how it works in practice.
- Continuous and specialized monitoring
With SOCaaS, the company gains access to 24/7 monitoring by specialized analysts who monitor the environment in real time. This eliminates exposure windows and drastically reduces the mean time to detect (MTTD) incidents.
- Intelligent event correlation
Instead of isolated alerts and excessive noise, SOC-as-a-Service uses advanced event correlation, threat intelligence, and behavioral analysis to identify real risks. This improves accuracy and reduces false positives.
- Rapid incident response
Response speed is one of the most critical factors in cybersecurity. An outsourced SOC already operates using established playbooks, processes, and automations, reducing mean time to resolution (MTTR) and minimizing financial and operational impacts.
- Less reliance on in-house labor
The in-house IT team is no longer burdened with highly specialized tasks. The SOC-as-a-Service acts as a strategic extension of the team, allowing the company to focus on its core business.
- Scalability and cost predictability
The "model as a service" approach allows you to scale protection as your business grows, without requiring a large upfront investment. Costs are predictable and proportional to the monitored environment.
- Ongoing adoption of best practices
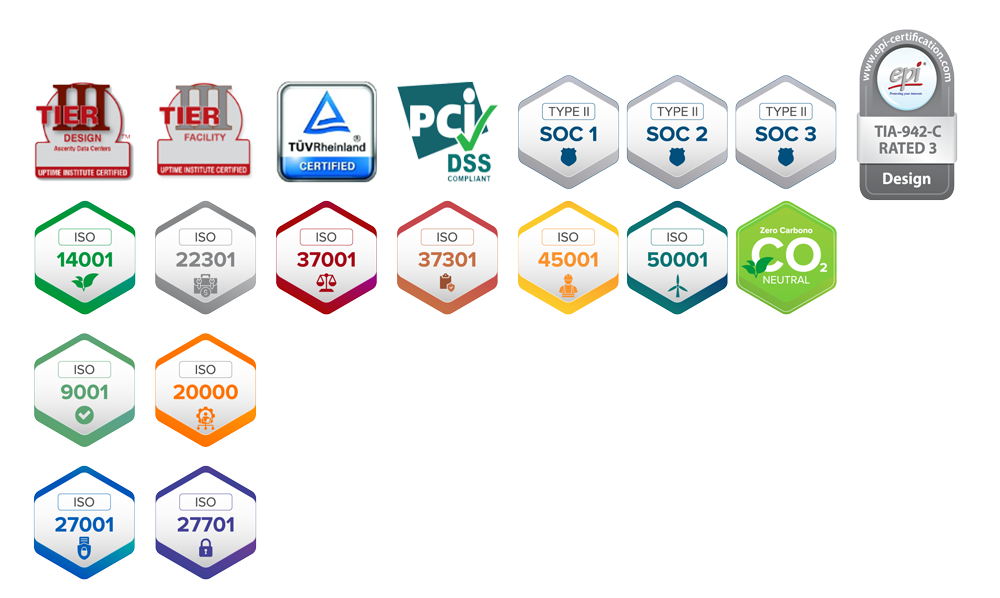
SOC-as-a-Service providers operate in accordance with frameworks such as NIST, MITRE ATT&CK, ISO 27001, and LGPD, ensuring continuous improvement of their security posture.
SOC as a Service and Regulatory Compliance
Another critical issue for many companies is compliance with standards and regulations. Sectors such as healthcare, finance, manufacturing, and retail face increasingly stringent data protection requirements.
SOC as a service directly contributes to:
- Compliance with the LGPD;
- Security audits;
- Evidence of ongoing monitoring;
- Incident logging and traceability;
- Improvement of internal controls.
This reduces legal, financial, and reputational risks.
For which companies is SOC-as-a-Service ideal?
Although SOC is often associated with large corporations, the "as a service" model makes this structure accessible to medium-sized companies and growing organizations as well.
SOCaaS is particularly well-suited for companies that:
- They do not have a dedicated in-house security team;
- are migrating to the cloud or already operate in the cloud;
- They work with sensitive data;
- They need to improve their security maturity quickly;
- Have suffered from or want to avoid ransomware attacks;
- They must comply with regulatory requirements.
Regardless of size, the key benefit remains the same: advanced security without operational complexity.
SOC-as-a-Service as part of a broader security strategy
It is important to note that SOC-as-a-Service does not operate in isolation. It integrates with other key layers, such as:
- Immutable backup;
- Disaster Recovery;
- Secure private cloud;
- Identity management;
- Endpoint protection.
When integrated into a well-designed security architecture, the SOC becomes the nerve center of the operation, ensuring visibility, control, and continuous response.
Conclusion
The evolution of cybersecurity requires more than just tools: it requires processes, people, and continuous operations. For most companies, attempting to build all of this in-house results in high costs, operational risks, and unnecessary complexity.
SOC-as-a-Service emerges as a strategic alternative, enabling organizations to rapidly improve their security maturity, reduce risks, and respond to threats in a professional manner—all without overburdening the IT department or turning security into a bottleneck for the business.
In a landscape where attacks are inevitable, the difference lies in the ability to detect, respond to, and recover from them quickly. And that starts with visibility, expertise, and continuous operation.
If your company is looking for greater security, more control, and less complexity, SOC-as-a-Service is a key step on that journey. Learn more!






Comments are closed