Data Protection
Did you know that the most modern ransomware attacks go straight to your backups and then encrypt your data? And when this happens, your company is UNABLE to restore the backup.
In the current scenario, cyber threats are evolving every day and regulatory requirements have never been stricter. To maintain business continuity and protect your most sensitive information, it is essential to adopt a complete solution that guarantees solution that guarantees:
- Integrity of your data
- Availability even after incidents
- Confidentiality at all times
Security, Reliability and Resilience for the Digital Future
When it detects any anomalies - such as backup failures, suspicious increases in data volume or unauthorized access attempts - the system triggers automatic alerts via email, SMS or integration with collaboration tools, allowing your team to act immediately to correct the problem before it impacts the business.
Our Main Features
Integration of disaster recovery, cloud backup and workload mobility. All orchestrated and automated.
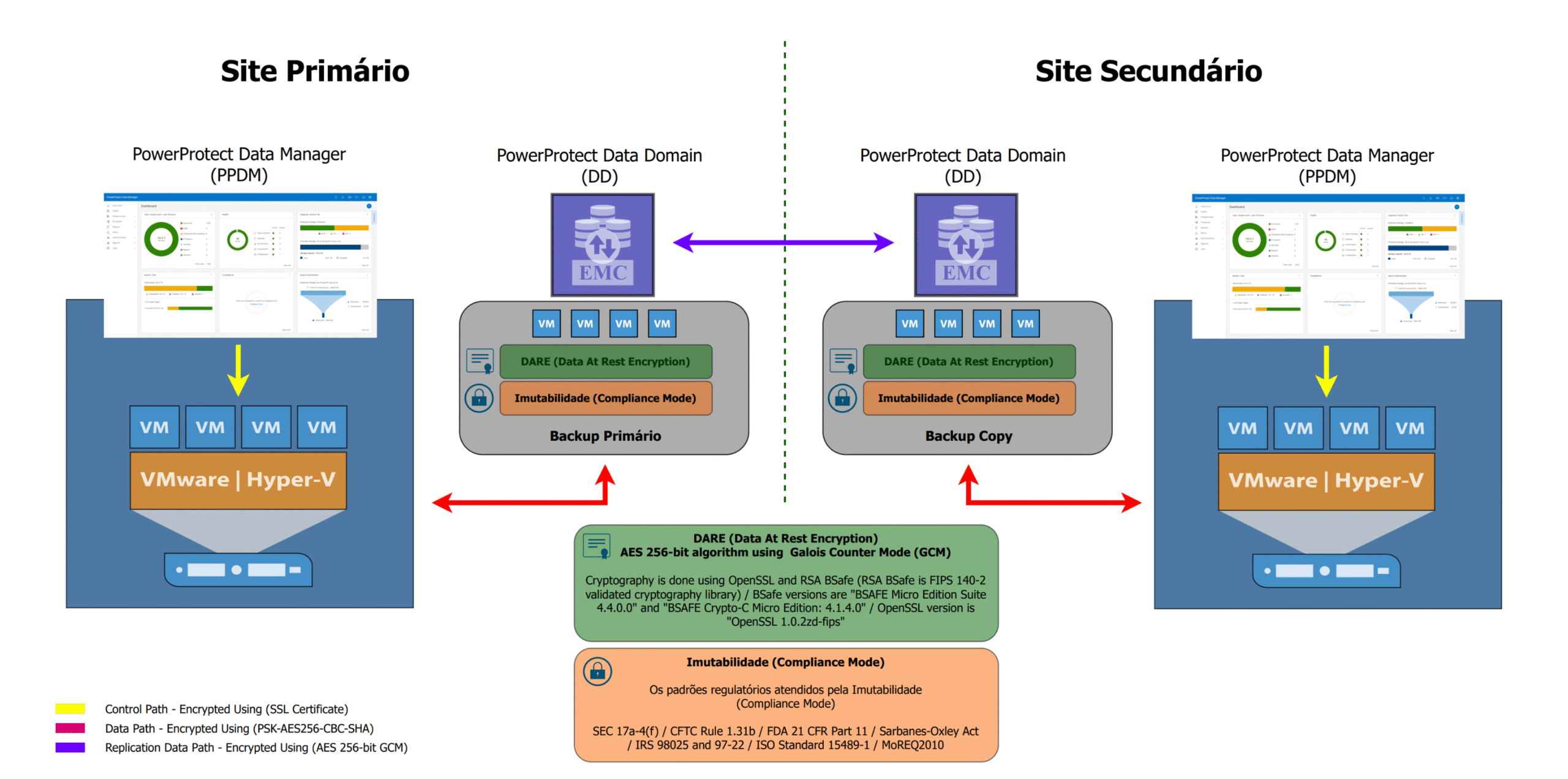
All your backed-up information is protected by FIPS 140-2 encryption, ensuring that even in the event of a physical breach, your data remains inaccessible to attackers.
During backup, recovery or replication transmissions between datacenters, your data is encrypted end-to-end, preventing interception on public or private networks.
Immutability (Retention Lock) - Compliance Mode
With Compliance Mode, we apply a retention block that prevents any alteration or deletion of data until the established legal deadline, complying with regulations such as GDPR and LGPD and protecting you against ransomware and internal incidents.
We make encrypted and authenticated copies via SSL certificates, ensuring that replicas of your backups, even in remote locations, are protected against man-in-the-middle attacks and unauthorized access.
Instant Recovery
When every second counts, our solution allows you to restore your systems and data almost immediately, minimizing downtime and guaranteeing the continuity of your services.
Proactive Monitoring and Smart Alerts
Our solution includes a continuous monitoring system that checks the integrity of your backups and the behavior of your IT environments in real time.
Why does it matter to your company?
Minimizing Operational Interruptions
By ensuring immutable backups and instant recoveries, you avoid long periods of downtime that can jeopardize sales, customer service and internal productivity. Less time offline means more efficiency and trust for your employees and partners.
Evolving Threat Protection
With end-to-end encryption and intelligent anomaly detection, your company will always be one step ahead of ransomware, intrusions and human error. It's not just about reacting to incidents, but preventing them before they cause financial or reputational damage.
Compliance and legal peace of mind
By adhering to international standards (GDPR, LGPD, HIPAA) and offering detailed audit reports, you eliminate the risk of fines and lawsuits. Your compliance team will have full visibility over retention and access policies, simplifying audits and ensuring transparency for customers and regulators.
Benefits for Your Company
Risk reduction
Protection against ransomware, leaks and critical failures.
Simplified Compliance
Reports and controls that facilitate audits.
High Availability
24/7 operation with almost instant recovery.
Scalability
Adaptation to data growth without loss of performance.
Who is this service for?
Medium and large companies (over R$100 million): who need robust, scalable solutions and need to stay one step ahead of cyber threats.
IT teams with a lack of resources: looking to strengthen governance and gain autonomy without overburdening the internal team.
Organizations facing audits: with regulatory requirements that do not tolerate security breaches and need to undergo IS audits.
Ready to Strengthen Your Security?
Contact us and find out how ADD IT Cloud Solutions can turn your IT environment into a digital fortress.
In addition to Data Protection, you can also access other solutions from ADD IT Cloud Solutions!
Want to know how Data Protection works?
Fill in the contact form and we'll get back to you.