Vulnerability Analysis
At ADD IT Cloud Solutions, we know that security is the foundation of any modern IT strategy. Our Vulnerability Analysis is a complete service, designed to identify, classify and remediate breaches in your entire infrastructure-from the physical datacenter to hybrid cloud environments-before they become real risks to your business.
What is Vulnerability Analysis?
It is the systematic process of scanning and evaluating IT assets (servers, applications, containers, networks and endpoint devices) for known flaws, insecure configurations or outdated code or firmware that could be exploited by can be exploited by hackers.
How we work
Integration of disaster recovery, cloud backup and workload mobility. All orchestrated and automated.
We inventory critical assets, categorize priorities and define the scope of the assessment with a focus on the components with the greatest impact on the business.
We use market-leading tools (Qualys, Tenable, Rapid7) and customized techniques to identify vulnerabilities across the entire stack: operating systems, middleware, web applications, APIs and cloud infrastructures.
We complement automatic results with manual validation of attack scenarios, reducing false positives and contextualizing threats according to your reality.
We apply CVSS metrics and map each vulnerability to its level of criticality, exploitation time and potential impact, so you know exactly where to act first.
We deliver a clear report with a technical description, evidence and practical recommendations - from code fixes to configuration adjustments and hardening policies.
After the patches have been implemented, we carry out a new round of tests to ensure that the vulnerabilities have been effectively mitigated.
Why does it matter to your company?
Proactive Protection
Instead of reacting to incidents, we anticipate and correct weak points, avoiding interruptions and financial losses.
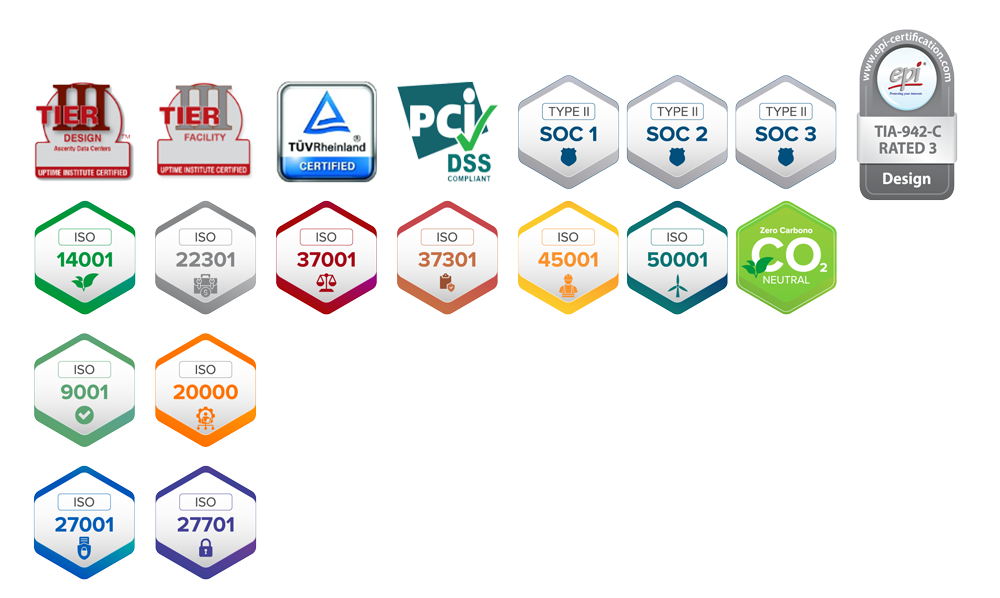
Strict Compliance
We meet the requirements of standards such as LGPD, ISO 27001, PCI-DSS and other industry regulations, reducing legal and reputational risks.
Market Confidence
Customers and partners value secure organizations with a competitive edge that reinforces their credibility.
Benefits for Your Company
Risk reduction
Less chance of serious incidents, ransomware or data theft.
Continuous Improvement
We integrate the results into your ISMS and DevOps continuous improvement process.
Cost optimization
Avoid fines, rework and unplanned downtime that can eat into your IT budget.
Total Visibility
Dashboards and executive reports that allow you to track progress and results.
Who is this service for?
Medium and large companies (over R$100 million): who need robust, scalable solutions and need to stay one step ahead of cyber threats.
IT teams with a lack of resources: looking to strengthen governance and gain autonomy without overburdening the internal team.
Organizations facing audits: with regulatory requirements that do not tolerate security breaches and need to undergo IS audits.

Request NOW a free evaluation of the asset scope you want to test.
In addition to Vulnerability Analysis, you can also access other solutions from ADD IT Cloud Solutions!
Want to know how Vulnerability Analysis works?
Fill in the contact form and we'll get back to you.