SIEM, UEBA, and SOAR: How These Technologies Work Together to Detect and Respond to Threats
Cybersecurity is no longer just a technical issue; it has become a strategic concern directly linked to business continuity. The rise of increasingly sophisticated attacks—such as ransomware, targeted phishing, and insider threats—has exposed the limitations of approaches based on isolated tools. In this scenario, the combination ofSIEM, UEBA, and SOARemerges as a modern and effective model for detecting, analyzing, and responding to security incidents, offering organizations greater visibility, intelligence, and agility.
The current challenge facing companies is directly linked to the complexity of IT environments. Hybrid infrastructures, cloud computing, SaaS applications, remote work, and multiple devices significantly expand the attack surface. At the same time, this scenario generates a massive volume of data and security alerts, making it difficult to identify what actually poses a risk. Among the main problems faced are an excess of irrelevant alerts, a lack of centralized visibility, difficulty in identifying suspicious behavior, and slow response times to critical incidents, in addition to the overload on security teams.
It is in this context that SIEM, UEBA, and SOAR complement one another and serve as the pillars of an integrated information security strategy.SIEM (Security Information and Event Management)forms the foundation of this ecosystem. Its primary function is to collect, centralize, and correlate logs and events from various sources, such as servers, firewalls, antivirus software, applications, cloud systems, and network devices. By bringing this information together in a single location, SIEM provides visibility into the environment and enables the identification of patterns and suspicious events.
In addition to centralization, SIEM generates alerts based on predefined rules and known patterns, and supports audits and regulatory compliance requirements. However, despite its importance, SIEM has a significant limitation: it relies heavily on rules and known signatures. This means that new attacks, subtle behaviors, or internal threats may not be detected effectively using this traditional model alone.
To overcome this limitation,UEBA (User and Entity Behavior Analytics) comes into play. Unlike approaches based solely on events, UEBA uses machine learning and behavioral analysis to understand what is considered normal within the organization’s environment. It analyzes the behavior of users, systems, devices, and applications over time, creating a behavioral baseline.
Based on this reference, UEBA can identify anomalies that indicate real risks, even if there is no known signature. Examples include users accessing critical systems outside of normal hours, a sudden increase in the download of sensitive data, attempts to access resources that have never been used before, or suspicious lateral movements within the network. This approach is particularly effective for detecting insider threats, compromised accounts, and advanced attacks that seek to operate silently.
One of the major benefits of UEBA is the reduction of false positives. By contextualizing events based on normal behavior, it helps filter out irrelevant alerts and prioritize only those that pose a real risk. When integrated with SIEM, UEBA enriches alerts, transforming raw data into actionable, risk-driven insights.
However, accurately detecting threats is only part of the challenge. The other half has to do with the speed and consistency of the response. This is whereSOAR (Security Orchestration, Automation, and Response)becomes essential. SOAR is responsible for orchestrating processes, integrating security tools, and automating incident responses through predefined playbooks.
In practice, SOAR enables the execution of automated or semi-automated actions, such as blocking malicious IP addresses, isolating compromised endpoints, disabling suspicious accounts, opening incident tickets, and notifying the responsible teams. By standardizing these responses, SOAR reduces reliance on manual actions, minimizes human error, and significantly accelerates threat containment time.
When SIEM, UEBA, and SOAR work together seamlessly, they create an intelligent security ecosystem. SIEM collects and correlates events, UEBA analyzes behavior and identifies real risks, and SOAR executes rapid and consistent responses. The result is a significant reduction in irrelevant alerts, greater accuracy in detecting advanced threats, faster responses, and a much more efficient use of IT and security teams’ time.
The benefits of this approach extend beyond the technical aspects. From a strategic perspective, integrating these technologies reduces financial risks associated with cyberattacks, such as operational downtime, regulatory fines, and reputational damage. Furthermore, it raises the organization’s cybersecurity maturity level, shifting it from a reactive to a proactive, data- and risk-driven approach.
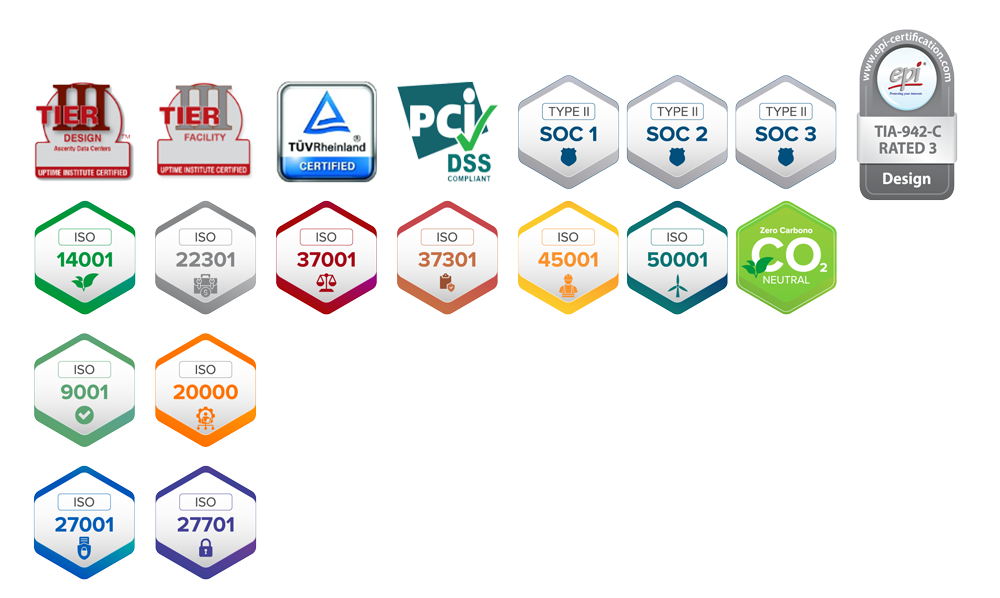
Another key benefit is scalability. With the automation provided by SOAR, it is possible to expand the IT environment without needing to proportionally increase the size of the security team. This feature is particularly important given the global shortage of cybersecurity professionals. In addition, log centralization, access traceability, and standardized responses facilitate audits, forensic investigations, and compliance with standards such as the LGPD, ISO 27001, and other regulations.
This integrated strategy is particularly well-suited for growing companies, organizations with hybrid or cloud environments, regulated industries—such as healthcare, finance, and law—and businesses that handle sensitive data or require high availability. In these contexts, security is no longer merely an operational cost but becomes a critical factor in competitiveness and trust.
In a modernSOC (Security Operations Center), SIEM, UEBA, and SOAR are considered fundamental pillars. A SOC that relies solely on manual monitoring tends to be reactive, overwhelmed by alerts, and slow to respond to incidents. By integrating these technologies, the SOC becomes data-driven, capable of prioritizing real risks, automating repetitive tasks, and focusing on strategic decisions.
One of the metrics most significantly impacted by this approach isMTTR (Mean Time to Respond), or the average time taken to respond to incidents. Modern attacks evolve rapidly: within minutes, malware can spread across the network; within a few hours, data can be exfiltrated; and in a short period, backups can be compromised. The SIEM, UEBA, and SOAR triad drastically reduces this time by enabling real-time detection, intelligent alert prioritization, and automated responses, turning hours or days into minutes or seconds.
Another significant benefit is the reduction in alert fatigue. An overload of irrelevant notifications is one of the biggest challenges faced by security teams, as it increases the risk of critical incidents going unnoticed. With the support of UEBA and SOAR automation, the focus shifts from the volume of events to the actual risk to the business.
This integration also fosters a significant shift in mindset: security shifts from being focused solely on isolated incidents to being risk-based. Instead of merely asking whether an incident occurred, the organization begins to assess the potential impact of that behavior on the business, thereby facilitating communication with management and strategic decision-making.
In cloud and hybrid environments, this approach becomes even more important. The ability to centralize information, maintain visibility beyond the traditional data center, and automate responses across distributed infrastructures is essential for companies that have migrated to the cloud but need to maintain control, security, and compliance.
In short, modern cybersecurity requires intelligence, integration, and automation. The combination of SIEM, UEBA, and SOAR enables more accurate threat detection, a deeper understanding of the actual context of risks, and rapid incident response—protecting data, operations, and reputation. In a landscape of increasingly sophisticated attacks, investing in this integrated approach is an investment in business continuity and resilience.Learn more!






Comments are closed