We know that the pandemic period and the need to work remotely have exponentially accelerated digital attacks and threats and, in order to stay safe, organizations have also increased their investments in cyber security.
To give you an idea, according to data from Apurathere was a 394% increase in cyber threats in 2020, with companies registering more than 275 million incidents.
On the other hand, IDC estimates that worldwide spending on security tools and solutions will reach 133.7 billion dollars by 2022.
Generally speaking, cyber security can be defined as a series of practices and strategies whose main objective is to protect the information, technologies and agents that make up a company.
These solutions are crucial for guaranteeing the integrity of all the organization's assets, minimizing the risk of intrusions or even data theft, as well as ensuring total corporate governance.
In this scenario, companies can also achieve compliance with the LGPDreducing the chances of fines and other sanctions provided for by law in the event of data leaks or incidents.
However, for cyber security initiatives to be effective, certain processes are crucial. See below what they are and how to implement them effectively.
You may be interested: Private cloud: how to protect your company from cyber?
5 steps to maximize your company's cyber security
Among the main processes for maximize your company's security of your company, we can mention:
1. draw up a disaster recovery plan
The disaster recovery is nothing more than a documentation of how a company should respond if an unexpected situation occurs, be it of any nature, with the aim of minimizing the impacts and re-establishing the IT infrastructure.
Good planning must take into account all the characteristics of your business, which involves the number of users and the number of assets (be they equipment or systems), as well as the company's objectives.
In turn, this process must always act preventively, which means that all internal information must be backed up periodically, minimizing the risk of loss.
2. Establish and monitor strategic indicators
Next, define strategic indicators to be monitored by your IT team, which should cover everything from network access to the imputation of malicious files or suspicious browsing.
Nowadays, it's possible to rely on tools that automate this monitoring of the entire infrastructure and make the day-to-day life of professionals easier.
3. Guide your employees correctly
With a plan in hand, as well as a privacy policy and good security practicesit's time to pass them on to your employees, which includes creating "strong" logins, constantly updating internal systems and using equipment correctly.
Guidance is crucial to minimize threats due to human error and ensure that everyone in the company "speaks the same language".
4. Have a centralized and standardized operation
An IT operation is only mappable when it is standardized and has centralized management. This means that your organization needs to have the appropriate tools and practices in place to enable unified management.
In addition, it is crucial that the entire IT team follows a standard for creating new users, deadlines, validation, monitoring and other network activities. This makes it much easier to find bottlenecks or identify situations that are out of the ordinary.
5. Rely on a specialized company
Finally, count on a specialized company to help you manage your infrastructure.
A partner has the expertise to optimize your business and guarantee the highest possible performance without affecting your security.
See also: Ensure more security and productivity with a cloud server for small businesses
Meet add it Cloud Solutions!
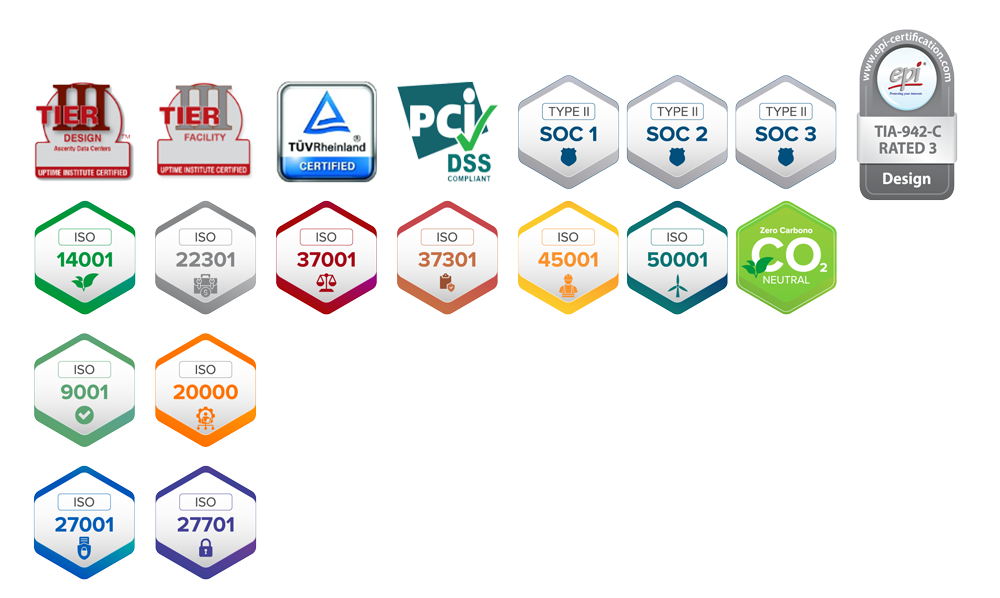
Add it Cloud Solutions can help you optimize your business's cyber security. With over 20 years of experience in the sectorwe offer cloud and cyber security solutions for your business.
With technical and specialized professionals, we help your organization design, implement and sustain a disaster recovery plan, ensuring that your company is always available and secure.
In addition, our cloud solutions have state-of-the-art tools for data protectionminimizing the risk of threats to your business.
Want to know more? Log in now and talk to our team.






Comments are closed