Reduce Cyber Risks by up to 95% with multi-layer protection
In an increasingly competitive and regulated business environment, IT is no longer just a cost center, but a strategic vector for innovation. However, the growing adoption of hybrid and multicloud architectures poses significant challenges for IT managers: dispersed governance makes it difficult to see assets, while the lack of skilled labor drives up operating costs and increases the chances of critical failures. In addition, legislation such as LGPD, GDPR, PCI-DSS and HIPAA require strict controls over data storage and processing, on pain of million-dollar fines and reputational damage. In this context, ADD IT Cloud Solutions' private cloud infrastructure emerges as the answer to these pains, offering an environment designed to increase security, simplify management and maintain high performance at predictable costs.
To illustrate the urgency of this agenda, IDC studies show that by 2027 the volume of corporate data is expected to grow by 60%, while demands for 24×7 availability and compliance will jump by 50% in the same period. This "gap" between data growth and internal governance capacity means that many companies opt for specialized solutions, capable of delivering strict SLAs and dedicated expertise, without passing on the entire burden of maintaining highly trained internal teams.
Overview of ADD IT's Private Cloud Architecture
The basis of ADD IT's solution is a private cloud, built on Tier III standard datacenters strategically interconnected by a national fiber backbone. Internally, each client receives an isolated environment, custom-configured and protected by multiple layers of defense:
- Multi-layer security
- NGFW for deep packet inspection;
- WAF + ADC to protect and optimize web applications;
- DDoS mitigation in real time;
- Centralized SIEM for correlation and automatic response.
- High Availability & Performance
- Geo-redundant HA clusters;
- 100% NVMe storage with guaranteed IOPS;
- Low latency network with IXPs and Tier 1 providers.
- Management & Compliance
- Alignment with the NIST Cybersecurity Framework;
- 24×7 monitoring, patches and managed upgrades;
- Customized ISMS audit reports for LGPD, ISO 27001, PCI-DSS and HIPAA.
This modular architecture allows organizations to scale vertically and horizontally, adapting resources according to business seasonality or access peaks, without interruptions and with predictable charges.
Security Layers
2.1 NGFW (Next-Gen Firewall)
The NGFWs implemented by ADD IT perform application inspection, behavior analysis and identity control, blocking known threats and detecting anomalous patterns that escape traditional solutions. This includes blocking zero-day exploits and segmenting internal traffic, mitigating lateral movement by attackers.
2.2 WAF (Web Application Firewall) and ADC (Application Delivery Controller)
For critical web applications (e-commerce, customer portals, APIs), the WAF defends against SQL injections, Cross-Site Scripting (XSS) and other layer 7 vulnerabilities. In parallel, the ADC optimizes traffic, balancing load and reducing latency, guaranteeing fast responses even during peak access times.
2.3 DDoS mitigation with Wanguard
The Wanguard solution continuously monitors traffic at the edge of the network, identifying volumetric attacks and triggering automated filters before malicious traffic reaches the customer's environment. In real tests, peaks of 300 Gbps were neutralized in less than 30 seconds, with no impact on availability.
2.4 Centralized SIEM
By centralizing firewall logs, operating systems, databases and applications, ADD IT's SIEM offers:
- YES: collection and normalization of logs;
- SEM: real-time correlation, alert generation and automated playbooks;
- SOAR (optional): orchestration of immediate responses to incidents.
This set increases security maturity, making it possible to meet audit requirements and respond to incidents in minutes rather than hours.
High Availability and Performance
3.1 Redundant HA Clusters
Each workload runs on redundant clusters, distributed across multiple racks and datacenters. If one physical node or entire rack fails, another takes over automatically, guaranteeing failover in less than 60 seconds and maintaining SLAs above 99.9%.
3.2 NVMe storage
By fully migrating to NVMe, ADD IT has achieved latencies below 500 μs and throughput above 4 GB/s in standard configurations. Transactional databases and data analysis environments benefit from this performance, reducing processing time and licensing costs.
3.3 Low Latency Network
The infrastructure is connected to IXPs in São Paulo, Rio de Janeiro and Fortaleza, with redundant links between locations. This reduces average latency for customers across the country to less than 20 ms, ideal for response time-sensitive applications such as VoIP and algorithmic trading.
Customer Isolation and Personalized Management
4.1 Dedicated environment
Each client operates in a "sanctuary" of isolated resources - segmented VMs, storage and networking, with no overlap with other clients. This eliminates "noisy neighbors" and prevents security risks in multi-tenant environments.
4.2 Custom Configuration
ADD IT's solutions team conducts requirements workshops, maps dependencies and designs customized architecture, ensuring that the solution meets the performance, compliance and budget needs of each business.
4.3 24×7 support and operation
With in-house staff certified in AWS, VMware, Microsoft and security partners, ADD IT provides:
- Proactive monitoring;
- Management of planned patches and upgrades;
- 24/7 call center with critical response time SLAs.
This frees up the client's internal team to focus on innovation rather than infrastructure maintenance.
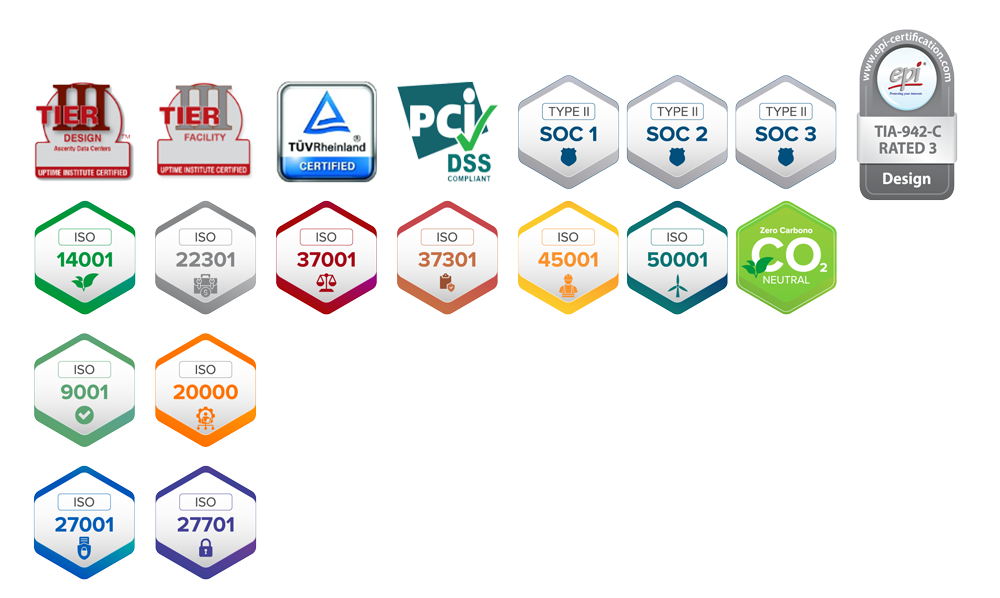
Compliance and Audits
The infrastructure already incorporates controls and policies aligned with the NIST Cybersecurity Framework, covering Identify, Protect, Detect, Respond and Recover functions. Among the main artifacts available:
- Asset inventory with criticality classification;
- Access policies based on RBAC and mandatory MFA;
- Log reports and audit-ready evidence;
- Encryption in transit and at rest with managed keys.
Companies in the financial, health and government sectors, often subject to PCI-DSS, HIPAA and ISO 27001 audits, find this solution a differentiator for reducing internal compliance efforts by up to 70%.
Use Cases and Practical Benefits
6.1 Protection against Ransomware
IBM reports reveal that the average cost of a ransomware attack in 2024 exceeded US$4.5 million. With encrypted, immutable backups and restore tests, ADD IT ensures that critical data can be recovered in minutes, minimizing operational damage.
6.2 Business Continuity
Availability SLAs above 99.9% ensure that ERPs, CRMs and automation systems never go down, protecting companies' revenues and reputations.
6.3 Flexible scalability
Customers with dynamic needs have already reported a 40% reduction in the time it takes to provision new servers for seasonal peaks, without the need to invest in their own data center in advance.
6.4 Cost optimization
Through predictable billing models and the elimination of CAPEX, companies have eliminated 30% of their IT spending, adjusting resources according to real demand.
Read also at: evolution-of-ransomware-hamas
Conclusion and Next Steps
ADD IT Cloud Solutions delivers a complete infrastructure that unites:
- Multi-layered security and advanced monitoring;
- High availability with automatic failover;
- Cutting-edge performance based on NVMe and optimized networking with speeds of 40Gbps;
- Dedicated environments and 24/7 management;
- Compliance ready for rigorous audits;
- National presence with low latency throughout Brazil.
If your organization is looking to reduce risks, ensure continuity and gain agility in infrastructure expansion, and also reduce IT costs by up to 40%, talk to our experts today:
- Free diagnosis of your current environment;
- Personalized proposal and fixed price;
- Assisted migration plan at NO cost, with no risks and no downtime.
Turn your IT into a strategic differentiator with ADD IT - start today and guarantee security, high performance and peace of mind for your business. Find out more!






Comments are closed